
Now isn’t the time to fall for cybersecurity myths!
It won’t come as a surprise to hear that, in 2022, cyberattacks are continuing to grow more sophisticated and frequent. Today’s digital landscape makes it more important than ever for organizations and individuals to protect themselves against the most common types of threats. Unfortunately, a handful of cybersecurity misconceptions are still holding too many people back from taking the necessary action to safeguard their sensitive information.
To make sure your data security practices are up-to-date, in this blog we take a look at 5 of the most common cybersecurity myths and offer solutions on how to overcome them.
Cybersecurity Myth 1: Passwords Alone Are Enough to Protect You
Passwords can no longer be solely relied upon to keep your data safe. While strong passwords are essential, cybercriminals may still find ways to hack them. So, if you want to implement robust cybersecurity measures, it’s crucial that you construct a multilayered defense.
When thinking about how to layer your data security, a great starting point is to implement multi-factor authentication (MFA). MFA is an authentication method that requires you to provide multiple types of verification to gain access to a resource. Find out how to deploy 2-factor authentication on your computer with our how-to video.
Cybersecurity Myth 2: Deleting Files Is Enough
‘Deleting’ a file from your computer doesn’t actually make it disappear. In other words, when you move a file to the Recycle Bin and then empty it, you are not truly erasing anything. Instead, there will be a lasting trail of data that remains on your hard drive, for example, in the temporary files folder.
This trail is known as residual data, or data remanence, and it can be easily recovered by third parties with the use of widely available file recovery software. The same issue applies to your browsing history, which won’t be permanently deleted when it’s just cleared with your web browser.
So, how do you permanently delete files? On active computers, the best practice is to use data wiping software to delete files and data remanence for good. When a hard drive reaches the end of its life, it’s recommended to wipe it entirely for proper data sanitization; physically destroying it isn’t enough. Learn more about using data wiping software to delete files permanently with our ultimate guide.
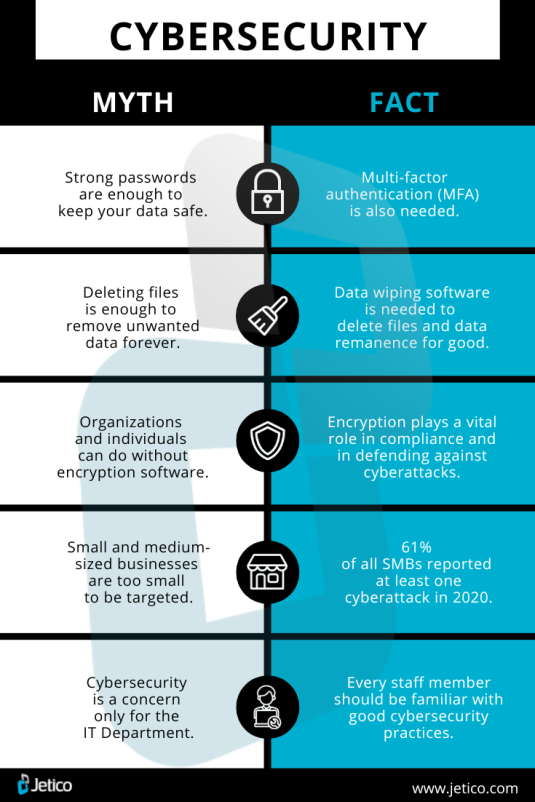
Cybersecurity Myth 3: Encryption Solutions Aren’t Worth It
It’s regrettable that some organizations and individuals retain the opinion that encryption software is something they can do without. Whether they view encryption as being too complicated or expensive for their needs, this is a misconception that can really come back to bite you in the form of a completely avoidable data breach. Particularly for organizations, encryption should play a vital role in defending against cybercriminals and ransomware attacks.
To address some of the common criticisms of encryption, good software is generally very simple to use and will not impact the performance of your systems. As for the cost of encryption, it would be a mistake to avoid paying for software to save money. Let’s face it, the price of encryption software is negligible compared to potential losses from data breaches or ransomware, as well as fines resulting from falling short of compliance regulations like GDPR.
Cybersecurity Myth 4: Small and Medium-Sized Businesses Aren’t Targeted
One classic data security myth is that small and medium-sized businesses (SMBs) are not often the victim of cyberattacks. The thoughts behind this probably come from SMB owners assuming that their data is not particularly valuable, therefore it’s not worthwhile for cybercriminals to pursue.
Unfortunately, this opinion is simply false. According to the 2021 Data Breach Investigations Report from Verizon, 61% of all SMBs reported at least one cyberattack during the previous year. Another report, this time from Barracuda Networks, found that small businesses are 3 times more likely to be targeted by cybercriminals than larger companies.
Whether SMBs are specifically targeted due to typically less robust security measures, or they are just unlucky victims of cybercriminals looking to attack anything and everything, the end result is that SMBs need to take the necessary steps to protect themselves.
Cybersecurity Myth 5: Data Security Only Concerns the IT Department
Of course, IT teams have a big responsibility when it comes to protecting their organization’s data. But it could be argued that the biggest security threat to a business or organization is its own employees. According to the 2022 Data Breach Investigations Report from Verizon, 82% of data breaches in 2021 involved a human error. “Whether it is the use of stolen credentials, phishing, misuse, or simply an error, people continue to play a very large role in incidents and breaches alike,” the report says.
So, while IT departments do what they can to protect in-house data, their hard work should be combined with wider organizational changes to take security measures to the next level. For instance, clear data protection policies should be implemented and security awareness training should be provided to all employees.
Time to Strengthen Your Data Security
Now that you’ve seen the light when it comes to these 5 common cybersecurity myths, there’s no longer any excuse to neglect the safeguarding of your organization or personal system. To learn more, why not check out our ultimate guide to enterprise data protection?
