Centrally Managed Encryption with BestCrypt Volume Encryption
Centrally manage disk encryption & SSO with more authentication control
Read Our Latest News
Take Command of All Disk Encryption Activities with Jetico Central Manager, Now Also Available for Cloud.
Available for both Windows and Mac, BestCrypt Volume Encryption – Enterprise Edition offers an ideal encryption solution for offices with mixed OS environments.
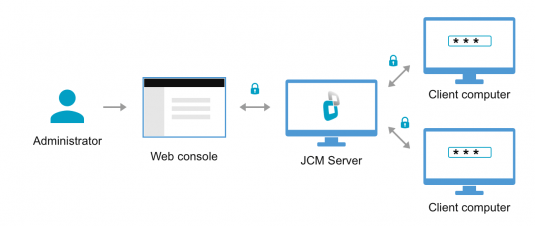
Jetico Central Manager (JCM), included as a component in BestCrypt, enables a single person (Administrator) from a central administration computer to always monitor usage of encrypted data on remote workstations across an enterprise network.
Jetico Central Manager also includes a database for gathering and storing information from client computers, such as log information about deployment and updates of BestCrypt Volume Encryption client modules or rescue information to recover encrypted data in case of emergency.
To learn more about JCM or require a free trial, contact us!
Features – BestCrypt Volume Encryption – Enterprise Edition
Deployment
Deploy with Ease
- Connect client computers to the server and add them to the database automatically by simply running one
executable file - Support for deployment automation using Windows Group Policy or third-party utilities (e.g., Microsoft SCCM, LANDesk) (Windows only)
Management
Remote Endpoint Encryption
- Control encryption activities from anywhere – now with any device with a web-browser, including smartphones and tablets
- Manage encryption on any remote computers including those outside your corporate network as long as it has internet connection
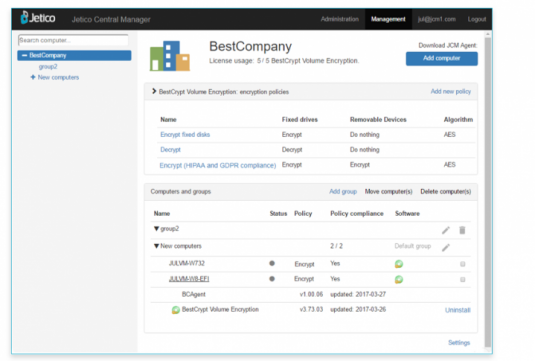
Central Management of Encryption Policy Distribution
- Gain peace of mind with Pre-set encryption policies based on compliance requirements, including HIPAA and GDPR
- Create customized encryption policies to best match their company standards, taking advantage of Single Sign-On (SSO), Trusted Platform Module (TPM) and encrypting used space only
- On client side, end user only needs to enter/set password to initiate encryption as configured by Administrator in JCM
Central Management of Encryption with SSO & More Authentication Control
- Admins have additional control of the authentication process on client computers, including Single Sign-On (SSO), password strength settings, custom boot-time prompt and unattended restart (Windows only)
Control User Access to Encryption/Decryption of Disk Volumes
- Administrator decides whether to allow users to ‘Manage Encryption Locally’ or force their computers to abide by a central policy
Centralized Security Policies for Removable Drives
- Encrypt removable drives, such as USB sticks, and set individual security policies for non-encrypted removable drives to be read-only or forbidden entirely
Monitoring
Monitor State of Client Computers
- Get instant alerts about any problems and see the progress of encryption tasks in real time
- Use dashboards for real-time visibility into encryption activities and tracking of key cybersecurity metrics.
Centralized Logging
- Get detailed logs of selected computers or a group of computers – including full list of changes and instantly view warnings/errors
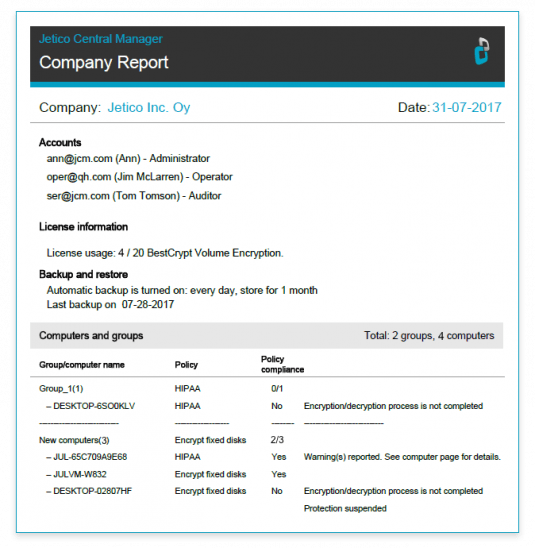
Create Global Reports in HTML or PDF Format
- Run and retrieve encryption reports for auditing purposes, including comprehensive information about: active accounts, status and number of licenses, status and number of managed endpoints, account activity logs
Audit Logs
- Review audit logs to trace back configuration changes made by a selected account or all accounts with complete and precise activity reporting
Task Automation
Recovery
- Automatically acquire the latest recovery information from client computers in JCM Database to allow security administrators to regain access to encrypted client data in case of emergency or forgotten password
Updating Software
- Schedule automatic updates for both client software and Jetico Central Manager Database
Backup
- Automatic backup of Jetico Central Manager Database
Security
Protected Network Traffic
- Communication between client computers and a server is secured by using public/private key technology with HTTPS protocol
Encrypted Database
- Sensitive information in Jetico Central Manager Database is securely encrypted
Encrypted Endpoints
- Client computers are encrypted with the strongest encryption algorithms recognized worldwide: AES, RC6, Twofish, Serpent and Camellia with 256-bit key depending on the encryption policy
MSPs & Bigger Enterprises
Server Clustering
- Cluster mode allows setting up several application servers and one control unit to distribute the load. Cluster mode is useful when managing large numbers of encrypted endpoints
Role-Based Administration
- Support for multiple accounts and role-based access control to share responsibilities between multiple personnel and assign access to Jetico Central Manager Console based on role (Administrator, Operator, Auditor)
Managing Multiple Companies
- MSP can now manage multiple companies from one database and a single console, including separate licensing, software and/or encryption policies
Learn more:
Contact us to get a free trial
New features in Enterprise Edition v.5
Quick Start guide
Full User Manual (Online)
Full User Manual (Online) – Cloud