Protection against ransomware
BestCrypt Data Shelter protects folders according to the policy selected by the user for this folder. In addition, the software also protects the folder from ransomware. A ransomware program is a malicious program (malware) that usually encrypts information and then demands a "ransom" for decrypting it. It can infiltrate a computer as a Trojan and then modify (usually encrypts) files or entire volumes on a disk.
BestCrypt Data Shelter protects against both types of ransomware at the file level and at the disk volume level.
File level protection
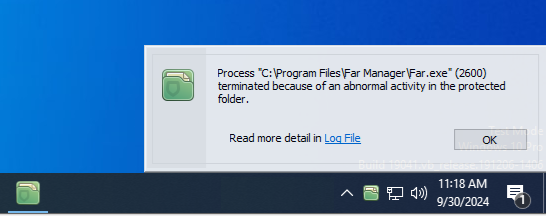
This type of protection is always active, it does not depend on the folder protection policy. If any Trojan tries to encrypt a protected folder, BestCrypt Data Shelter will display the following window and shut down the Trojan.
|
|
|
|
Disk volume level
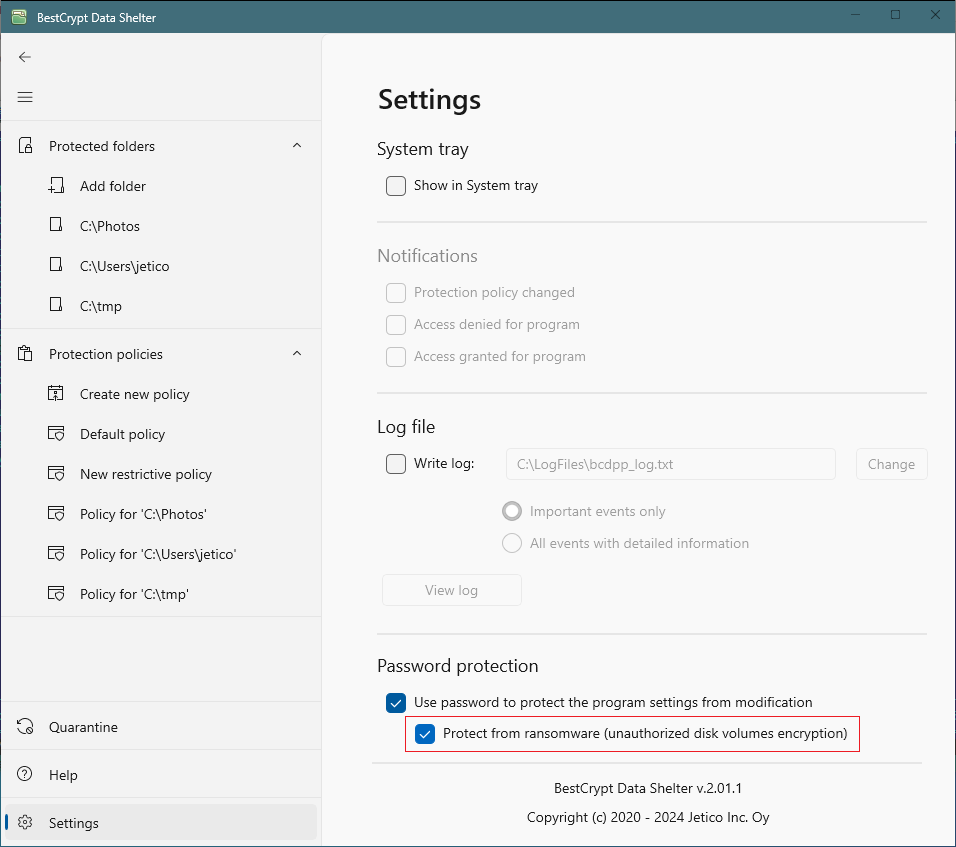
At the disk level, BestCrypt Data Shelter protects not only selected folders, but also entire volumes on the disk. To do this, the software requires the user to set password protection, as explained in the article Password protection for the program settings. As soon as you set password protection, the Protection against ransomware (unauthorized disk volumes encryption) checkbox becomes available, and you will be able to set this option.
|
|
|
|
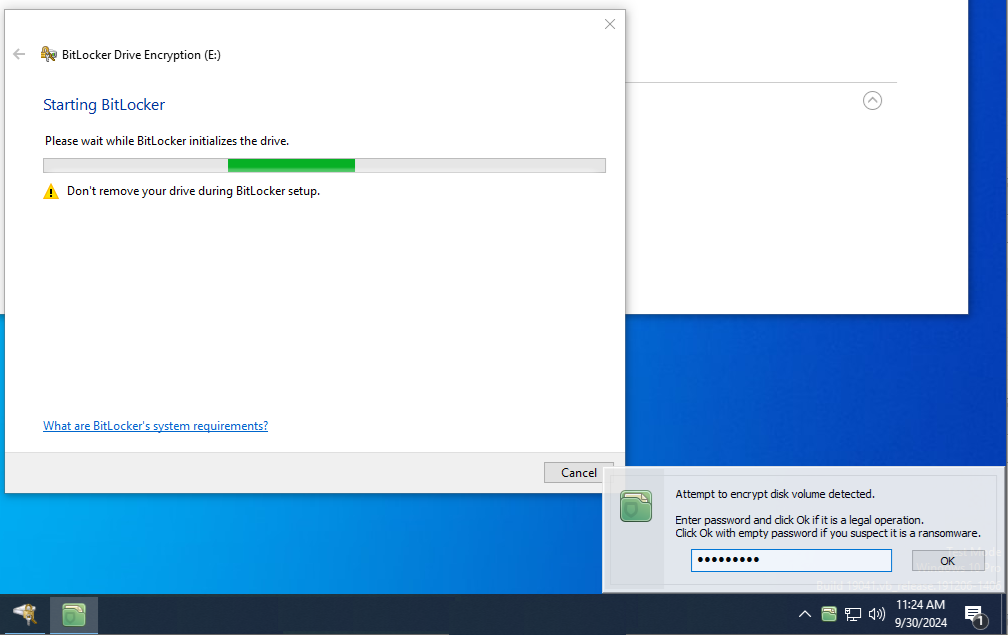
Password protection is necessary to verify whether the encryption request is from a legitimate user, or it is a Trojan or someone unwanted who has gained remote access to your computer. For example, if you run Microsoft BitLocker to encrypt a disk volume, BitLocker will be suspended, and BestCrypt Data Shelter will inform you about the encryption and ask you to enter a password.
|
|
|
|
If you do not enter the password and click Ok, the BestCrypt Data Shelter program will suspend BitLocker until the computer restarts. It is safer to suspend the encryption process than to end it to avoid data corruption.
If you enter the password, BitLocker will continue to work normally and successfully encrypt the disk volume.
Behavior of suspended encryption programs
Please note that encryption programs (both legal and Trojan) behave differently when their attempt to encrypt a disk volume is suspended:
- The first group of programs simply waits while BestCrypt Data Shelter expects the user to enter a valid password. Microsoft BitLocker and Jetico Volume Encryption are examples of such programs. The programs perform disk-level encryption completely asynchronously from other disk-level operations of the operating system. As a result, even if the encryption program is suspended, the operating system can work normally.
- The second group of programs forces the operating system to wait until they encrypt part of the disk volume. It is their way of avoiding the operating system's access to the disk, while they change sectors on the disk. As a result, as soon as BestCrypt Data Shelter suspends such a program, the entire operating system freezes. DiskCryptor is an example of a program that works this way. In this case, if you are going to encrypt your disk volume using DiskCryptor, please temporarily disable protection against ransomware in the BestCrypt Data Shelter.
Please note that the protection of BestCrypt Data Shelter does not depend on the specific software. It uses its own algorithm that allows it to detect the encryption of disk volumes in a general way, regardless of which program tries to run it. According to our tests, such encryption programs are not only effectively suspended, but also are not able to encrypt any sectors or damage the information inside them.
See also: